[SOLVED] ELI5: How to put several servers on one external IP?
-
You'll need to direct that port for the given service in the router control panel.
For your current server you have a port forwarding for that port already. Just add a port forwarding rule for the new service.
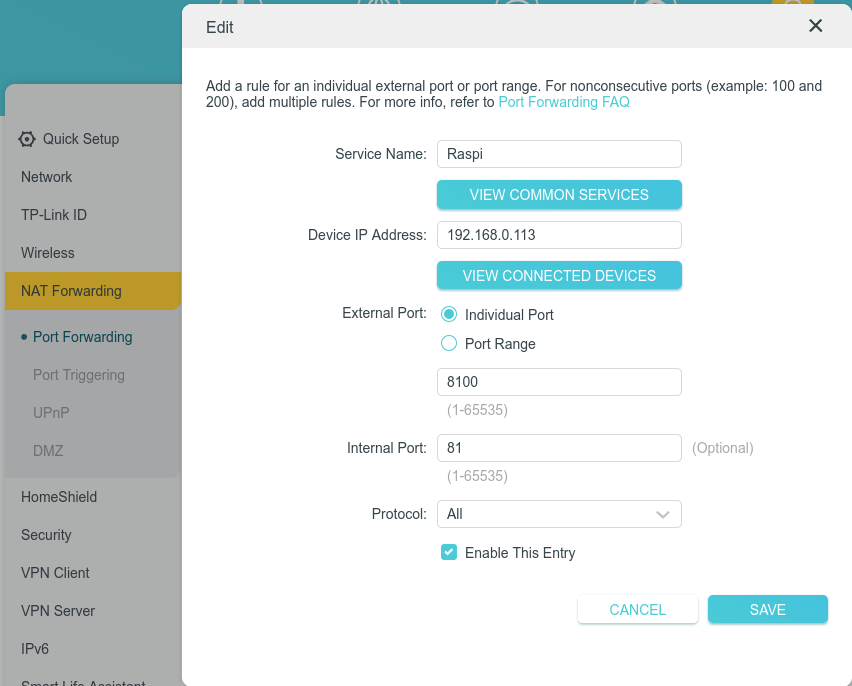
wrote last edited by [email protected]Tried doing that - here's how I've set it up:
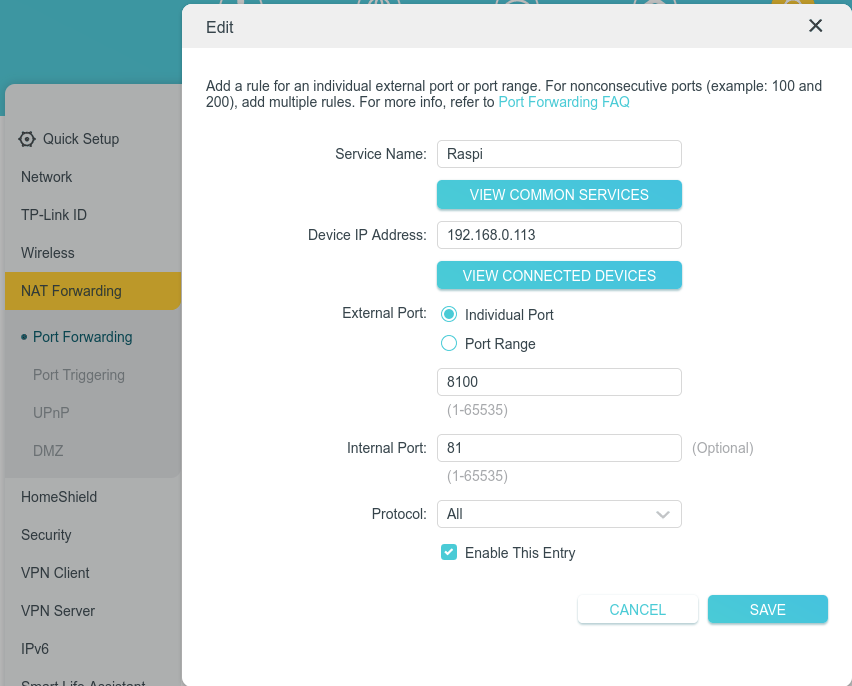
Expected behavior: now when I enter <my domain>:8100, I reach 192.168.0.113:81
Real behavior: connection times out
-
Tried doing that - here's how I've set it up:
Expected behavior: now when I enter <my domain>:8100, I reach 192.168.0.113:81
Real behavior: connection times out
wrote last edited by [email protected]Stupid question, but is the service reachable at all? What if you map 81 to 81? Or whichever port the other, confirmed-to-work service uses? What if you map that other service to 8100?
-
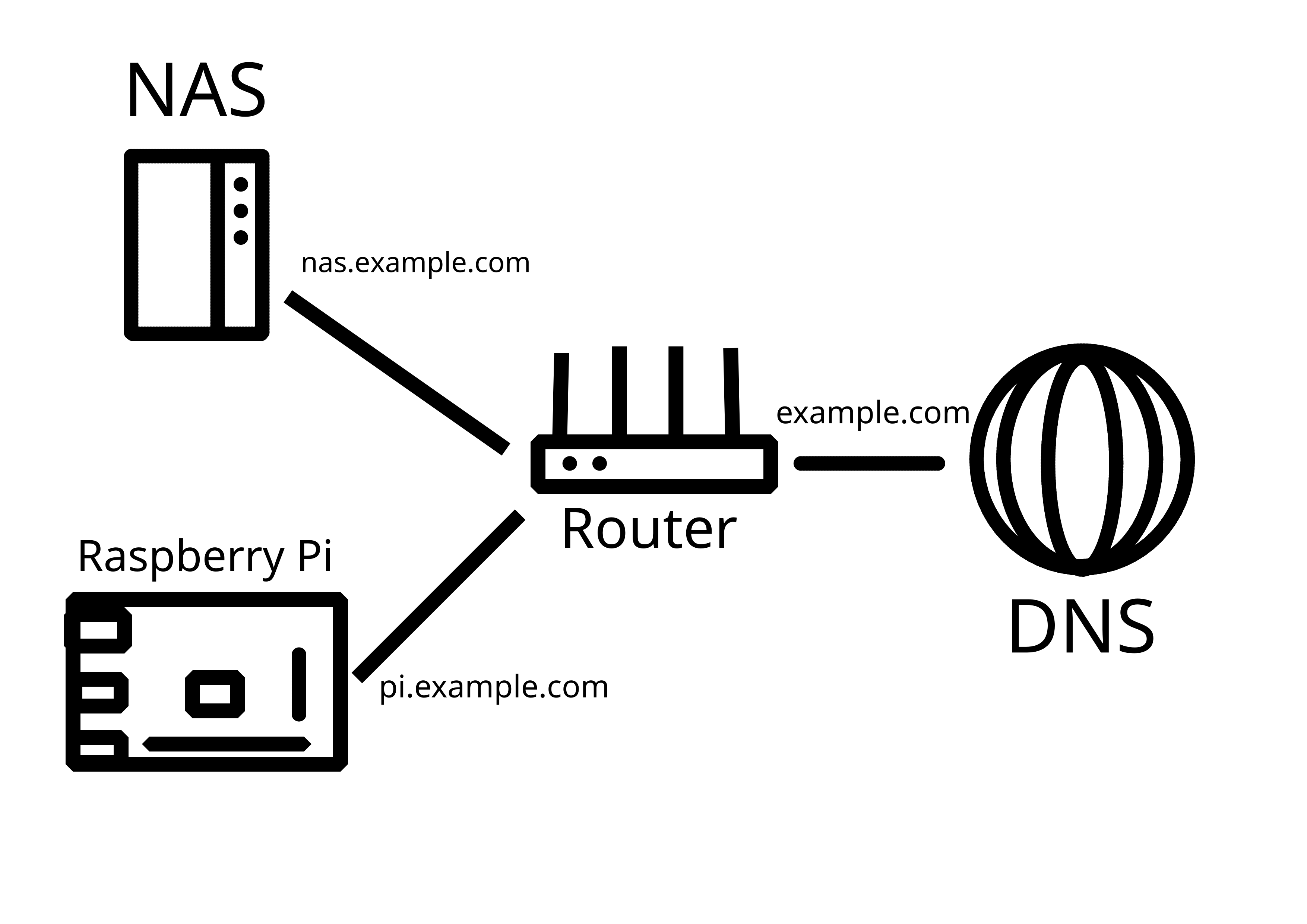
I'm pretty new to selfhosting and homelabs, and I would appreciate a simple-worded explanation here. Details are always welcome!
So, I have a home network with a dynamic external IP address. I already have my Synology NAS exposed to the Internet with DDNS - this was done using the interface, so didn't require much technical knowledge.
Now, I would like to add another server (currently testing with Raspberry Pi) in the same LAN that would also be externally reachable, either through a subdomain (preferable), or through specific ports. How do I go about it?
P.S. Apparently, what I've tried on the router does work, it's just that my NAS was sitting in the DMZ. Now it works!
Honestly Cloudflare Tunnels could be a very simple way to do it. I've always had tremendous luck with it. By using CF you can let them do all the heavy lifting instead of hosting your own... as long as you trust them.
-
You need a reserve proxy. That's a piece of software that takes the requests and puts them toward the correct endpoint.
You need to create port forwards in the router and direct 80 and 443 (or whatever you're using) toward the host of the reverse proxy and that is listening to on those ports. If it recognized the requests are for nas.your.domain, it will forward the requests to the NAS.
Common reverse proxies are nginx or caddy. You can install it on your raspberry, it doesn't need it's own device.
If you don't want that, you can create different port forwards on your router (e.g. 8080 and 8443 to the Raspi) and configure your service on the Raspi corresponding. But it doesn't scale well and you'd need to call everything with the port and the reverse proxy is the usual solution.
There's an issue with that first part. Do I configure it right? Should <domain>:8100 be redirected to 192.168.0.113:81 in this case?
-
Honestly Cloudflare Tunnels could be a very simple way to do it. I've always had tremendous luck with it. By using CF you can let them do all the heavy lifting instead of hosting your own... as long as you trust them.
They are a plague with how prevalent they have become.
The internet shouldn’t put all its eggs into one basket.
It’s just another centralized entity which will lead to monopolized power. It goes against what we are trying to do with federated networks like Lemmy and mastodon.
-
Stupid question, but is the service reachable at all? What if you map 81 to 81? Or whichever port the other, confirmed-to-work service uses? What if you map that other service to 8100?
wrote last edited by [email protected]Reachable through LAN, but not by URL, even if I port 81 to 81
P.S. Solved! NAS was sitting in the DMZ and this broke forwarding.
-
If you have a prosumer router I suggest you to use the ddns in the router plus a reverse proxy. This would be the cleanest solution.
If you can not, once everything is working with your external access to the synology, the dsm has a built-in reverse proxy so it can redirect http requests to another server. Although this proxy is really simple and limited it can get the work done if you setup is simple enough.
Thanks! Syno one didn't work properly, but I got it to work through different means
-
Reachable through LAN, but not by URL, even if I port 81 to 81
P.S. Solved! NAS was sitting in the DMZ and this broke forwarding.
What if you try reaching it through your public IP?
-
What if you try reaching it through your public IP?
wrote last edited by [email protected]Worked eventually, was about DMZ for my NAS
-
There's an issue with that first part. Do I configure it right? Should <domain>:8100 be redirected to 192.168.0.113:81 in this case?
External 80 to internal 80 and external 443 to internal 443
With this config you don't have to deal with ports later, as http is 80, https is 443 by default.
If you run some container on port 81, you have to deal with that in the reverse proxy, not in the router. E.g. redirect something.domian.tld to 192.168.0.103:81
If you use docker check out nginxproxymanager, it has a very beginner friendly admin webui. You shouldn't forward the admin ui's port, you need to access it only from your lan.
-
There's an issue with that first part. Do I configure it right? Should <domain>:8100 be redirected to 192.168.0.113:81 in this case?
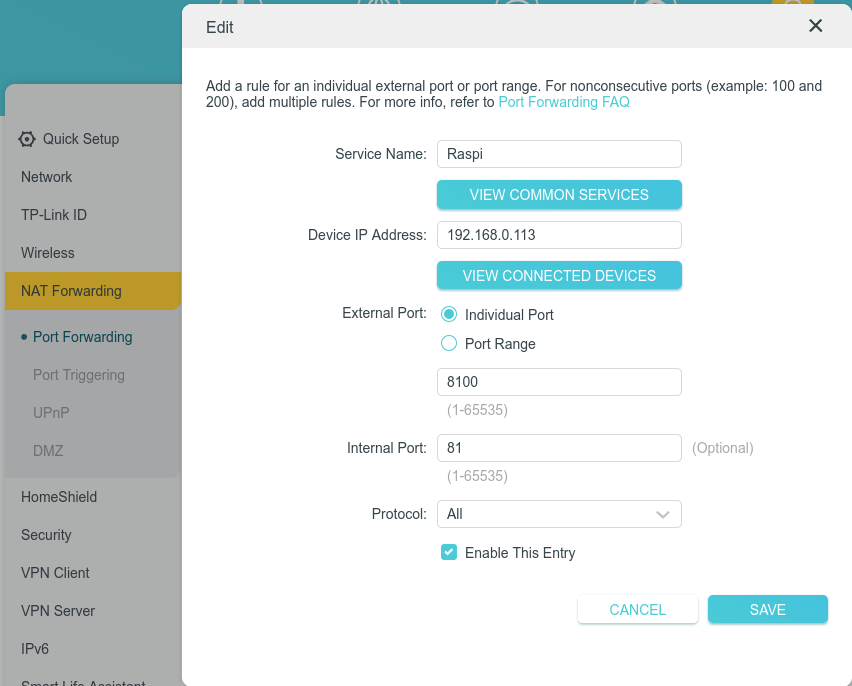
This only guarantees your WANip:8100 will map to 192.168.0.113:81, and doesn't address whether or not dns resolution is correct. I would also be weary of using port numbers on wikipedia's known ports list, as some ISPs will filter those upstream. The last thing is that your router may not want to hairpin that traffic, so if you're not coming in from the outside it might not be a valid test.
-
Honestly Cloudflare Tunnels could be a very simple way to do it. I've always had tremendous luck with it. By using CF you can let them do all the heavy lifting instead of hosting your own... as long as you trust them.
wrote last edited by [email protected]You can use frp to do the same thing a CloudFlare tunnel does without giving them your unencrypted data.
-
External 80 to internal 80 and external 443 to internal 443
With this config you don't have to deal with ports later, as http is 80, https is 443 by default.
If you run some container on port 81, you have to deal with that in the reverse proxy, not in the router. E.g. redirect something.domian.tld to 192.168.0.103:81
If you use docker check out nginxproxymanager, it has a very beginner friendly admin webui. You shouldn't forward the admin ui's port, you need to access it only from your lan.
wrote last edited by [email protected]Actually, I do - 81 is exactly the default port for nginx proxy manager. I just tried to expose it as a testing example, and already closed it back after a success (apparently port forwarding worked just fine, it's just that DMZ messed with it)
And since we're talking about this, what do I do with it next? I have it on my Pi, how do I ensure traffic is distributed through it as a reverse proxy? Do I need to expose ports 80 and 443 and then it would work automagically all by itself?
-
Honestly Cloudflare Tunnels could be a very simple way to do it. I've always had tremendous luck with it. By using CF you can let them do all the heavy lifting instead of hosting your own... as long as you trust them.
wrote last edited by [email protected]While not supportive of Big Tech, I do appreciate your piece of advice, and understand self-hosting needs differ!
P.S. Also beware, seems like there's a new attack through Tunnels:
-
This only guarantees your WANip:8100 will map to 192.168.0.113:81, and doesn't address whether or not dns resolution is correct. I would also be weary of using port numbers on wikipedia's known ports list, as some ISPs will filter those upstream. The last thing is that your router may not want to hairpin that traffic, so if you're not coming in from the outside it might not be a valid test.
Thanks for the pieces of advice! Yes, I tried to connect from external (mobile) network as well.
-
While not supportive of Big Tech, I do appreciate your piece of advice, and understand self-hosting needs differ!
P.S. Also beware, seems like there's a new attack through Tunnels:
Thanks for the heads up!
-
I'm pretty new to selfhosting and homelabs, and I would appreciate a simple-worded explanation here. Details are always welcome!
So, I have a home network with a dynamic external IP address. I already have my Synology NAS exposed to the Internet with DDNS - this was done using the interface, so didn't require much technical knowledge.
Now, I would like to add another server (currently testing with Raspberry Pi) in the same LAN that would also be externally reachable, either through a subdomain (preferable), or through specific ports. How do I go about it?
P.S. Apparently, what I've tried on the router does work, it's just that my NAS was sitting in the DMZ. Now it works!
Who is externally reaching these servers?
Joe public? Or just you and people you trust?If it's Joe public, I wouldn't have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it's just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
-
Who is externally reaching these servers?
Joe public? Or just you and people you trust?If it's Joe public, I wouldn't have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it's just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
Just me and the people I trust, but there are certain inconveniences around using VPN for access.
First, I live in the jurisdiction that is heavily restrictive, so VPN is commonly in use to bypass censorship
Second, I sometimes access my data from computers I trust but can't install VPN clients on
Third, I share my NAS resources with my family, and getting my mom to use a VPN every time she syncs her photos is near impossible
So, fully recognizing the risks, I feel like I have to expose a lot of my services.
-
Actually, I do - 81 is exactly the default port for nginx proxy manager. I just tried to expose it as a testing example, and already closed it back after a success (apparently port forwarding worked just fine, it's just that DMZ messed with it)
And since we're talking about this, what do I do with it next? I have it on my Pi, how do I ensure traffic is distributed through it as a reverse proxy? Do I need to expose ports 80 and 443 and then it would work automagically all by itself?
You type the ip of the rpi on the router, so from an external call the router will forward it to the rpi. Or I don't know what is your question.
Things may seem automagical in the networking scene, but you can config anything the way you want. Even in nginxproxymanager you can edit the underlying actual nginx configs with their full power. The automagic is just the default setting.
-
I'm pretty new to selfhosting and homelabs, and I would appreciate a simple-worded explanation here. Details are always welcome!
So, I have a home network with a dynamic external IP address. I already have my Synology NAS exposed to the Internet with DDNS - this was done using the interface, so didn't require much technical knowledge.
Now, I would like to add another server (currently testing with Raspberry Pi) in the same LAN that would also be externally reachable, either through a subdomain (preferable), or through specific ports. How do I go about it?
P.S. Apparently, what I've tried on the router does work, it's just that my NAS was sitting in the DMZ. Now it works!
If you go with IPv6, all your devices/servers have their own IP. These IPs are valid in your LAN as well a externally.
But it's still important to use a reverse proxy (e.g. for TLS).